Your Network Never Sleeps — Neither Should Your Security
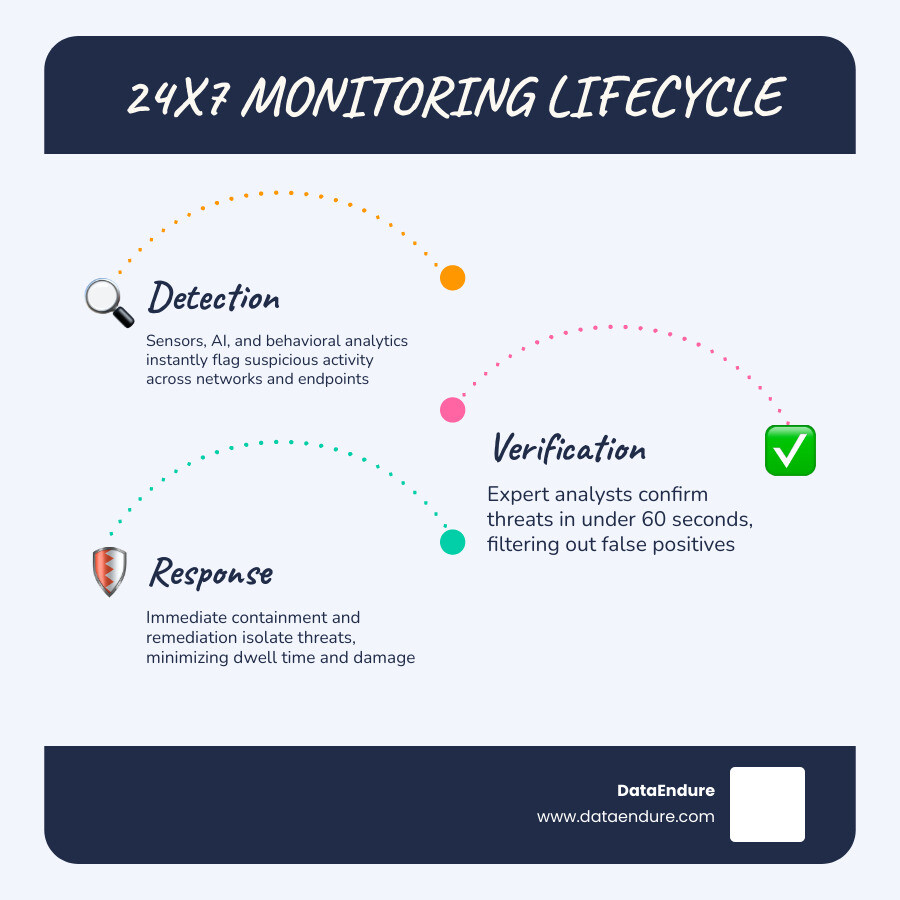
24×7 security monitoring is the continuous, round-the-clock surveillance of your IT environment — detecting, verifying, and responding to threats at any hour, including nights, weekends, and holidays.
Here’s what it means in practice:
- Detection: Sensors, AI, and behavioral analytics flag suspicious activity the moment it happens
- Verification: Trained analysts confirm whether a threat is real — typically within 60 seconds
- Response: Containment protocols activate immediately, isolating threats before they spread
- Recovery: Remediation steps begin right away, minimizing damage and downtime
The core difference from traditional security? Traditional systems alert. 24×7 monitoring acts.
If you’re an IT leader who has lived through a breach, you already know the worst part: you probably didn’t find out for hours. Maybe days.
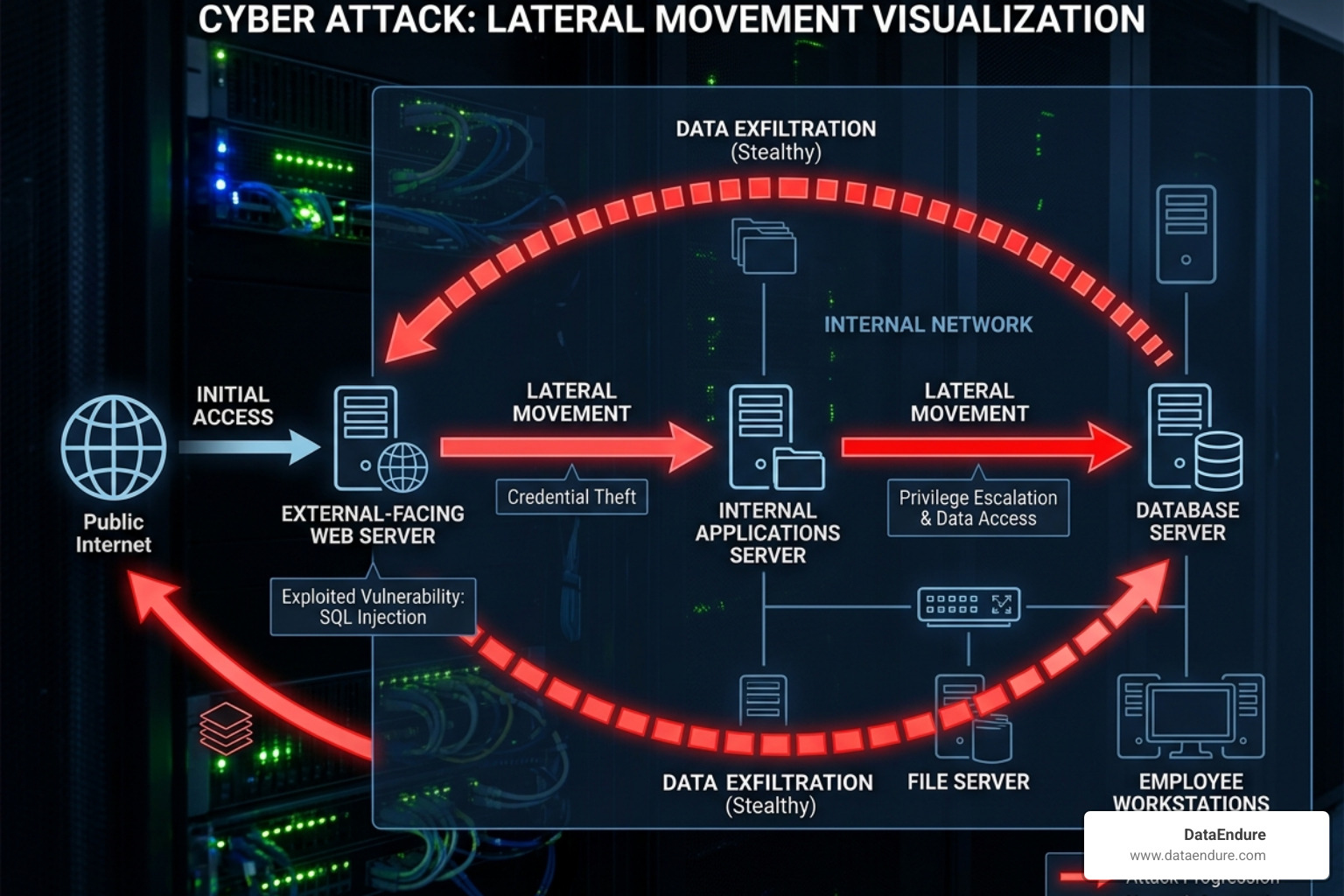
Threat actors know this. They deliberately launch attacks on Friday evenings, holiday weekends, and overnight — exactly when your team is thinly staffed or completely offline. Once inside, they move laterally through your network, quietly, buying time to exfiltrate data or deploy ransomware.
The exploitation of vulnerabilities as an initial breach path has nearly tripled in recent years. And when attacks land on a Friday, they take significantly longer to discover and contain — giving adversaries ample time to do serious damage.
The question isn’t whether your organization will be targeted. It’s whether anyone will be watching when it happens.
Defining 24×7 Security Monitoring in the Modern Threat Landscape
In the tech-heavy corridors of Silicon Valley and Santa Clara, we know that the “business day” is a polite fiction. While your office lights might go off at 6:00 PM, the digital world stays wide open. Modern 24×7 security monitoring isn’t just about having a digital “smoke alarm” that goes off when the building is already on fire; it’s about having a professional fire crew living in the building, ready to extinguish a match before it hits the carpet.
The threat landscape in May 2026 is more aggressive than ever. We’ve seen reports that threat actors are specifically timing their most destructive moves for when they know human oversight is at its lowest. In fact, U.S. federal agencies warned as recently as June 2025 of a sharp increase in state-sponsored cyberattacks designed to exploit these “off-hour” windows.
When an adversary exploits a vulnerability at 2:00 AM on a Saturday, they aren’t looking to make a loud entrance. They want to move laterally—slipping from one server to another, escalating their privileges, and identifying your most sensitive data. Without continuous monitoring, these intruders can enjoy hours or even days of “dwell time.” By the time your team logs in on Monday morning, the damage isn’t just done; it’s likely already been exfiltrated or encrypted.
Our DataEndure Managed Security Services are designed to close these gaps. By combining advanced sensors with human intelligence, we ensure that “off-hours” no longer exist for your attackers.
How 24×7 security monitoring impacts cyber insurance
If you’ve applied for or renewed a cyber insurance policy lately, you’ve likely noticed the paperwork is getting… intense. Carriers are no longer satisfied with a simple “yes” to having an antivirus. They want to see proof of mature, persistent defense.
24×7 security monitoring has become a cornerstone of insurability. Here is why:
- Premium Reduction: Many insurers offer significant discounts—sometimes up to 20%—for organizations that can prove they have professional, round-the-clock monitoring. It’s the digital equivalent of a “monitored alarm” discount on a homeowner’s policy.
- Compliance Mandates: Regulations like GDPR, CCPA, and various industry-specific standards often require rapid breach notification. You can’t notify authorities within 72 hours if you didn’t even know the breach happened until day four.
- Policy Approval: In some high-risk sectors in Silicon Valley, insurers are outright denying coverage to companies that lack a Security Operations Center (SOC) or a Managed Detection and Response (MDR) partner.
- Faster Claims: If a breach does occur, having a detailed log from a 24/7 monitoring service speeds up the forensic process, helping you get your claims processed and your operations back online faster.
For those navigating these complexities, our governance, risk, and compliance services provide the roadmap to meeting these rigorous standards.
Proactive threat hunting vs. reactive alerts
There is a dangerous myth in cybersecurity that “more alerts equal more security.” In reality, more alerts usually just lead to more coffee and more exhausted IT teams. This is known as alert fatigue, and it’s where many traditional security models fail.
Reactive alerts tell you that something already happened. A file was deleted. A password was changed. A firewall rule was bypassed.
Proactive threat hunting, which is a core component of modern MDR, looks for the “quiet” anomalies that don’t trigger a standard alarm. This involves:
- Identifying “Living off the Land” (LotL) techniques: Attackers often use legitimate system tools (like PowerShell) to carry out their dirty work. To a standard alert system, this looks like normal admin activity. To a 24/7 monitoring expert, the context of that activity might signal a breach.
- Behavioral Analytics: If a user who typically works 9-to-5 in Santa Clara suddenly starts accessing sensitive HR databases from an IP address in a different country at midnight, our systems flag that behavior immediately.
- Lateral Movement Detection: We watch for the subtle hops an attacker makes between systems, stopping them before they reach the “crown jewels” of your data.
The Strategic Benefits of Continuous Professional Oversight
Beyond just stopping the “bad guys,” 24×7 security monitoring provides a strategic advantage for businesses in competitive markets like Silicon Valley. It allows your internal IT team to stop playing “security whack-a-mole” and start focusing on projects that actually drive revenue.
Industry data suggests that sites and networks with professional monitoring have a 97% deterrence potential. Much like a physical security guard or a well-lit storefront, the mere presence of sophisticated, active monitoring often encourages opportunistic attackers to look for an easier target.
Furthermore, the operational savings are significant. Attempting to staff a 24/7 internal SOC requires at least 8 to 12 full-time employees to cover shifts, vacations, and sick days. For most mid-sized businesses, that payroll overhead is astronomical. By using DataEndure SOC-as-a-Service, you get elite-level protection at a fraction of the cost of building it yourself.
Advanced technologies powering 24×7 security monitoring
We aren’t just staring at screens all day (though we do plenty of that). Modern monitoring is a high-tech symphony of AI and human intuition.
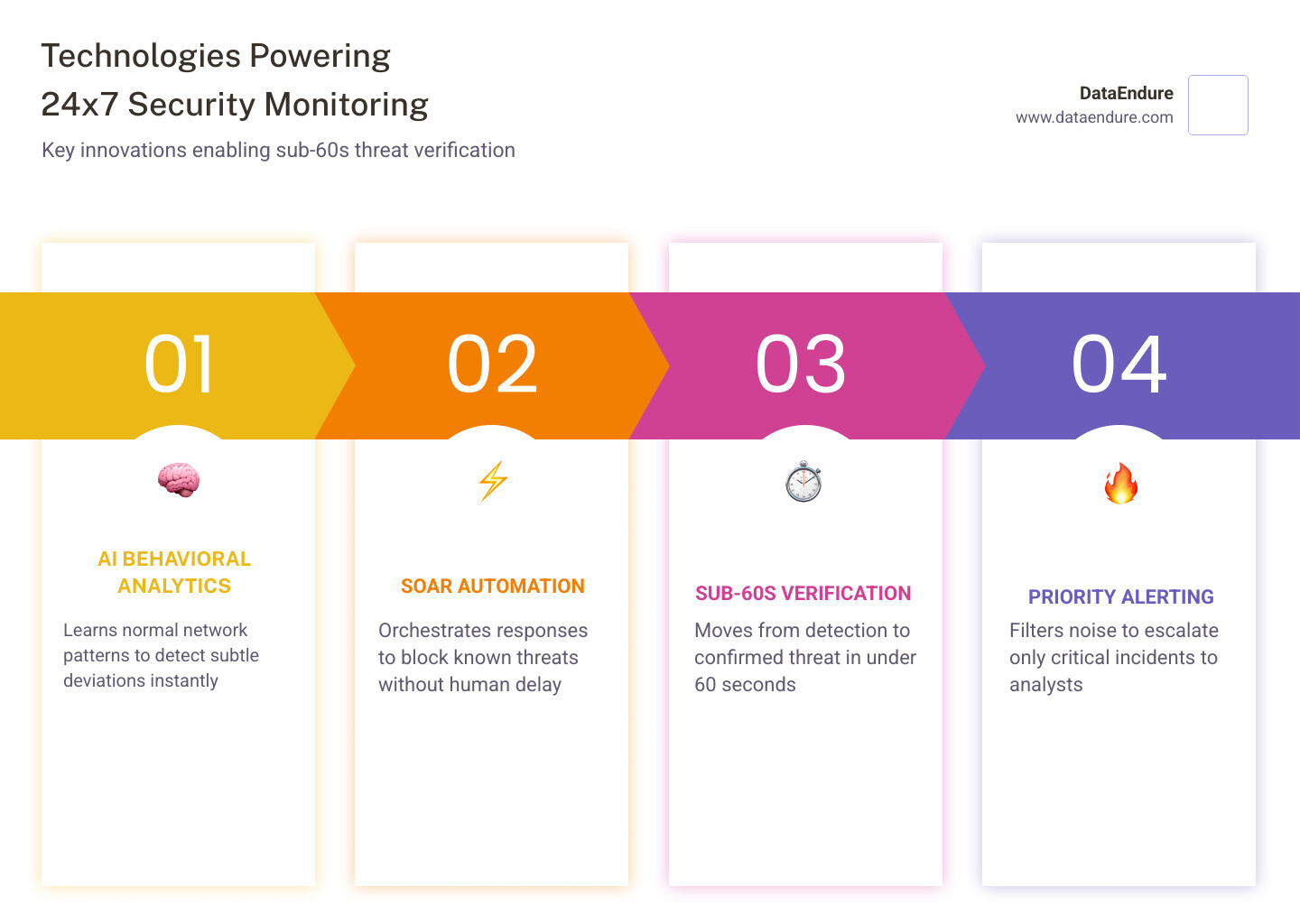
- AI-Driven Behavioral Analytics: Our systems learn what “normal” looks like for your specific network. When something deviates from that baseline, it’s flagged for review.
- SOAR (Security Orchestration, Automation, and Response): This allows us to automate the “boring” parts of security. If a known malicious IP tries to connect, the system can block it instantly without waiting for a human to click a button.
- Sub-60s Threat Verification: A minute is an eternity. Our goal is to move from detection to human verification in under 60 seconds.
- Priority Alerting: Not all alerts are created equal. Our technology filters out the “noise,” ensuring that when our analysts get a notification, it’s something that truly matters.
Rapid response and incident containment protocols
Detection is only half the battle. If you find a burglar in your house but don’t have a way to lock the doors or call for help, the detection hasn’t done you much good.
When our 24×7 security monitoring team identifies a legitimate threat, we follow a strict “Active Response” protocol:
- Isolation: We can instantly isolate an infected laptop or server from the rest of the network, preventing the “contagion” from spreading.
- Specialist Intervention: A human analyst—not a bot—takes over the investigation to determine the scope of the attack.
- Remediation: We work to remove the threat, whether it’s a malicious script, a compromised account, or a piece of ransomware.
- Dwell Time Reduction: By catching threats in minutes rather than days, we drastically reduce the “dwell time,” which is the primary factor in how much an incident will cost your company.
From Detection to Response: The Mechanics of Always-On Defense
How does this actually look in the real world? Let’s walk through a typical timeline of a Friday night attack.
Friday, 10:00 PM: An employee clicks a sophisticated phishing link while working late. A small piece of malware is installed. Friday, 10:02 PM: The malware attempts to “call home” to a command-and-control server. Our sensors detect this unusual outbound traffic. Friday, 10:03 PM: AI filters the alert, recognizing it as a high-priority threat. It automatically notifies our 24/7 SOC analysts. Friday, 10:04 PM: A DataEndure analyst reviews the activity. They see the lateral movement attempt and verify it’s a breach. Friday, 10:05 PM: The compromised workstation is isolated from the network. The threat is contained. Friday, 10:15 PM: Our team begins remediation and notifies your designated emergency contact.
Without 24×7 security monitoring, that malware would have had the entire weekend to spread across your servers, likely ending in a total network lockout by Sunday morning.
Addressing common challenges in 24×7 security monitoring
Maintaining a “never-sleep” defense comes with its own set of hurdles. We’ve spent years perfecting the ways we overcome them:
- Reducing False Positives: Nothing kills productivity like a security system that cries wolf. We use advanced machine learning to tune our sensors, ensuring that we only alert you when there is a real reason to worry.
- 100% Uptime: Our monitoring centers are built with redundancy. We have backup power, multiple internet providers, and geographically separated facilities. If one center goes down, another takes over without missing a beat.
- Integration: Your security shouldn’t be a “black box.” Our Security Operations team ensures that our monitoring integrates seamlessly with your existing cloud (Azure, AWS, Google) and on-premise infrastructure. We work with the tools you already have.
- Closing the Weekend Gap: By providing dedicated coverage during the times your team is most vulnerable, we eliminate the “Monday Morning Surprise” of discovering a weekend-long breach.
Comparing Costs: Managed SOC vs. In-House 24/7 Staffing
Let’s talk numbers. Many business leaders assume that “outsourcing” security is a luxury. In reality, for a 24/7 operation, it’s often the only financially viable option.
To run an in-house SOC in a high-cost area like Silicon Valley or Santa Clara, you aren’t just paying for one person. You’re paying for a full-scale operation.
| Expense Category | In-House 24/7 SOC (Estimated) | Managed 24/7 Monitoring (DataEndure) |
|---|---|---|
| Personnel | 8-12 Analysts (Salaries + Benefits) | Included in Service Fee |
| Training & Certs | Ongoing costs for specialized training | Included |
| Software/Tools | SIEM, EDR, SOAR licenses ($$$) | Included |
| Infrastructure | Physical space, redundant power/net | Included |
| Management | 24/7 shift supervisors | Included |
| Total Cost | $1.5M – $3M+ per year | 30–40% Lower TCO |
By choosing a managed model, you eliminate the payroll overhead for night, weekend, and holiday shifts. You also avoid the “hiring war” for cybersecurity talent in Silicon Valley—we provide the experts, so you don’t have to find, train, and retain them yourself.
Frequently Asked Questions about Constant Vigilance
How does 24/7 monitoring reduce alert fatigue?
Alert fatigue happens when your team is bombarded with thousands of low-level notifications. 24×7 security monitoring uses a combination of AI filtering and human expertise to act as a “sieve.” We catch the noise and only escalate the signals that represent a genuine threat. This means when we call you, you know it’s important.
Can 24/7 monitoring integrate with my existing tech stack?
Absolutely. Modern security shouldn’t require you to rip and replace everything you’ve already built. Our systems are designed to ingest data from your existing firewalls, endpoints, and cloud environments, providing a unified “single pane of glass” view of your security posture.
Why is monitoring essential for businesses during weekends and holidays?
Because hackers don’t take holidays. In fact, they love them. Statistics show that attacks launched on Fridays or before long weekends take significantly longer to discover and contain because internal IT teams are often at minimum capacity. 24/7 monitoring ensures that your defense is just as persistent as the threats you face.
Conclusion
In the fast-moving landscape of Silicon Valley, your data is your most valuable asset. Protecting it requires more than just a locked door; it requires a vigilant, expert eye that never blinks.
At DataEndure, we specialize in providing that “always-on” defense. We can deploy our managed security solutions in as little as 30 days, instantly upgrading your posture from reactive to proactive. Our skilled experts focus on detecting breaches in minutes, not months, effectively eliminating alert fatigue and giving you the peace of mind to focus on your business.
Don’t wait for a “Monday Morning Surprise” to realize your security needs an upgrade. Whether you’re looking to satisfy cyber insurance requirements or simply want to sleep better on Friday nights, we are here to help.
Secure your organization with DataEndure and ensure that while your network never sleeps, your security team is always wide awake.