When a Cyberattack Hits, Your SOC Is the Only Thing Standing Between You and Chaos
What does a security operations center do? Here’s the short answer:
| SOC Function | What It Means |
|---|---|
| Continuous Monitoring | Watches your entire IT environment 24/7/365 for threats |
| Threat Detection | Identifies suspicious activity across networks, endpoints, and cloud |
| Incident Response | Contains and neutralizes attacks before they spread |
| Log Management | Analyzes data trails to catch threats hiding in plain sight |
| Recovery & Remediation | Restores systems and investigates root causes after an attack |
| Compliance Management | Keeps your organization aligned with GDPR, HIPAA, PCI DSS, and more |
Hackers know something most IT teams don’t want to admit: most organizations never analyze their log data. That blind spot lets malware run undetected for weeks — sometimes months — before anyone notices.
A Security Operations Center (SOC) closes that gap.
It’s the combination of people, processes, and technology working together, around the clock, to monitor your environment and stop threats before they become disasters. Not just reacting — proactively defending.
In 2026, with the cyber threat landscape more aggressive than ever and the cybersecurity talent gap sitting at over 4 million unfilled positions globally, building that capability alone is harder than it sounds.
That’s exactly why understanding what a SOC does — and whether your organization has one — matters more than ever.
Defining the Nerve Center: What is a Security Operations Center?
At its simplest, a Security Operations Center (SOC) is the centralized “mission control” for an organization’s cybersecurity. It isn’t just a room full of screens (though those are cool); it is a unified function that employs a specialized team of experts, rigorous processes, and advanced technology to oversee an organization’s security posture.
Think of the SOC as the digital equivalent of a high-tech building security team. While a standard IT department focuses on making sure the “lights are on” and the “plumbing works,” the SOC is hyper-focused on the “burglars” trying to pick the locks or find an open window.
According to the Information security operations center overview, the primary objective is to provide situational awareness. This means knowing exactly what is happening across your servers, endpoints, cloud workloads, and network at any given second. In 2026, where digital transformation has expanded the attack surface into every corner of the business, having this centralized view is no longer a luxury—it’s a survival requirement.
SOC vs. NOC: Understanding the Difference
In our conversations with businesses in Santa Clara and across Silicon Valley, we often see people confuse the SOC with the Network Operations Center (NOC). While they might sit in the same building and share a love for caffeine, their missions are worlds apart.
A NOC is focused on performance and availability. They want to make sure the network is fast, the website is up, and the remote workers can connect to their VPN. If the network goes down, the NOC fixes it.
A SOC is focused on security and risk. They don’t care if the network is fast; they care if the traffic on that network is malicious. They monitor for signs of known exploits and suspicious activity that might indicate a breach.
| Feature | Network Operations Center (NOC) | Security Operations Center (SOC) |
|---|---|---|
| Primary Goal | Ensure network uptime and performance | Protect assets and detect/respond to threats |
| Main Metric | Speed, latency, and availability | Mean time to detect (MTTD) and respond (MTTR) |
| Key Question | “Is the system running?” | “Is the system under attack?” |
| Adversary | Hardware failure, congestion, human error | Cybercriminals, state actors, insider threats |
Core Functions: What Does a Security Operations Center Do?
If you’re asking what does a security operations center do on a daily basis, the answer is: a lot. The Security Operations Center (SOC): Structure and Functions | Information Security Authority highlights that the SOC acts as the first and last line of defense.
Its core functions can be broken down into several critical pillars:
- Asset Discovery and Inventory: You can’t protect what you don’t know exists. We start by identifying every server, laptop, database, and cloud service in your environment.
- Continuous Monitoring (24/7/365): Cybercriminals don’t take weekends off, and neither does a SOC. The team monitors the entire extended IT infrastructure—applications, system software, and computing devices—for signs of trouble.
- Log Management: Every action on a network leaves a trail. The SOC collects and analyzes these logs to find the “needle in the haystack” that signals an intrusion.
- Alert Ranking and Triage: Not every alert is a crisis. The SOC filters out the noise (false positives) so that the team can focus on the high-fidelity threats that actually matter.
Proactive Preparation and Attack Surface Reduction
A great SOC doesn’t just wait for the alarm to go off; it works to make the building harder to break into. This involves Security Operations Center (SOC): Structure and Functions | Information Security Authority tasks like vulnerability management and security refinement.
We perform routine maintenance, such as ensuring firewalls are updated and patches are applied. We also engage in behavioral monitoring. By establishing a baseline of what “normal” looks like in your network, we can quickly spot “abnormal” behavior, like a user logging in from a new country at 3:00 AM or a database suddenly trying to export 50GB of data.
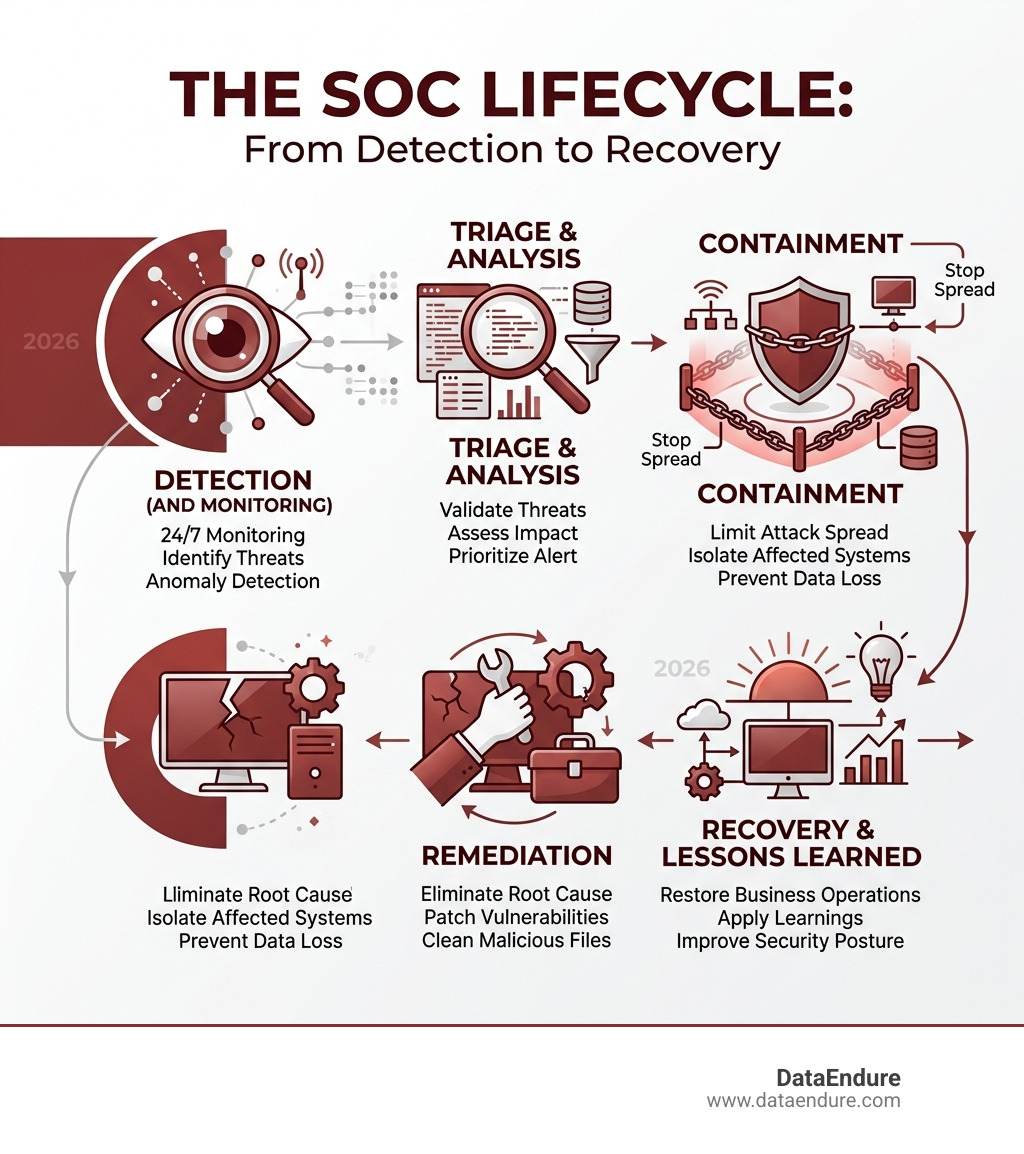
Real-Time Incident Handling and Recovery
When a threat is confirmed, the SOC shifts into high gear. This is where the incident response and recovery functions become vital.
- Triage: Determining the severity of the attack and its potential impact.
- Containment: Isolating affected systems to prevent the malware from spreading. This might involve shutting down specific network segments or suspending compromised user accounts.
- Remiation: Removing the threat, whether it’s deleting a malicious file or resetting credentials.
- Recovery: Restoring systems to their original state, which may involve wiping disks and restoring from backups.
The Human Element: Key Roles and Team Structure
While AI and automation are essential, the “secret life” of a SOC is still powered by human intelligence. The Security Operations Center (SOC) Roles and Responsibilities are often organized into tiers to ensure efficiency.
- SOC Manager: The “Chief of Police” for the digital world. They oversee the team, manage the budget, and ensure that security operations align with business goals.
- Tier 1 Triage Specialist: These are the first responders. They watch the monitors, sort through the alerts, and decide which ones need a closer look.
- Tier 2 Incident Responder: When a real threat is found, these experts jump in to investigate the scope of the attack and begin containment.
- Tier 3 Threat Hunter: These are the proactive detectives. They don’t wait for alerts; they actively search the network for hidden threats that might have bypassed automated defenses.
Specialized Expertise in a Modern SOC
As threats become more sophisticated, so do the roles within the SOC. A modern, mature center often includes:
- Forensic Analysts: They investigate the “digital crime scene” to understand exactly how a breach happened.
- Security Engineers: They build and maintain the tools the SOC uses, ensuring the technology stack is always optimized.
- Malware Reverse Engineers: They take apart viruses and ransomware to understand their code and how to stop them.
- Compliance Managers: They ensure every action the SOC takes is documented and aligns with regulatory requirements.
Modern SOC Technology and Delivery Models
To handle the sheer volume of data in 2026, a SOC needs a powerhouse technology stack. This usually starts with a SIEM (Security Information and Event Management) system, which aggregates data from thousands of sources into a single view.
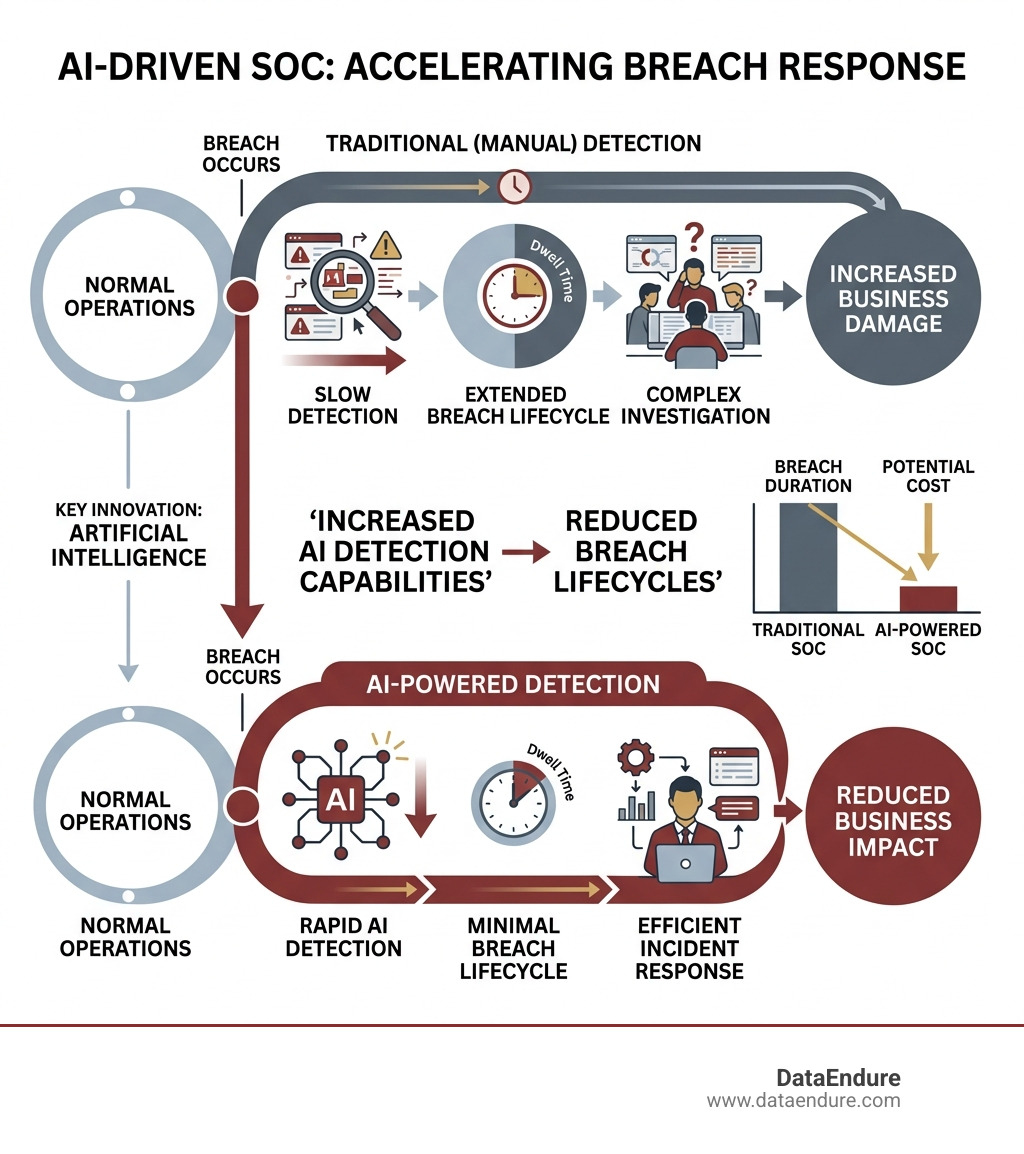
However, the modern SOC is moving toward XDR (Extended Detection and Response) and SOAR (Security Orchestration, Automation, and Response). These tools use AI-driven automation to handle repetitive tasks—like checking a suspicious IP address against a blacklist—at machine speed. This reduces “alert fatigue,” allowing our human experts to focus on complex problem-solving.
Choosing the Right Model: Internal, Outsourced, or Hybrid
One of the biggest questions businesses face is how to build their SOC. According to Security Operations Center (SOC): Structure and Functions | Information Security Authority, there are three main paths:
- Internal SOC: You build it yourself. This offers the most control but is incredibly expensive. Between the 24/7 staffing requirements and the high cost of Silicon Valley talent, the price tag is often out of reach for many.
- Outsourced SOC (Managed SOC/SOC-as-a-Service): You partner with a provider like DataEndure. We provide the experts, the tech, and the 24/7 coverage for a fraction of the cost of building it in-house.
- Hybrid SOC: A “best of both worlds” approach where you have a small internal team for day-to-day tasks but use an external partner for overnight monitoring or specialized incident response.
Overcoming Challenges and Ensuring Compliance
Running a SOC isn’t all high-fives and stopped hacks. The team faces massive challenges, starting with alert fatigue. When a system generates 10,000 alerts a day, it’s easy for a real threat to get lost in the noise. This is where DataEndure’s focus on reducing alert fatigue through skilled experts and automation becomes a game-changer.
Then there’s the data volume. In 2026, the amount of data generated by a standard business is staggering. Storing and analyzing that data requires massive computing power.
Finally, there is the ever-looming shadow of regulatory compliance. Whether it’s GDPR for European customers, HIPAA for healthcare, or PCI DSS for payments, the SOC is responsible for proving that the organization is protecting its data. A SOC provides the audit trails and documentation needed to keep the regulators happy and the business out of legal trouble.
Frequently Asked Questions about SOC Operations
What does a security operations center do for small businesses?
For small businesses, a SOC provides “big company” security on a small business budget. By using a SOC-as-a-Service model, small firms can access 24/7 monitoring and expert response that they could never afford to hire themselves. It allows them to focus on growth while we handle the digital defense.
How does a security operations center do threat hunting?
Threat hunting is the proactive side of the house. Instead of waiting for an alarm, analysts use “indicators of compromise” (IOCs) and advanced analytics to look for footprints left by hackers. It’s like a forest ranger looking for smoke before a fire actually breaks out.
What are the main benefits of having a SOC?
The biggest benefit is reduced dwell time. Without a SOC, a hacker can live in your network for over 200 days before being caught. A SOC aims to catch them in minutes. This protects your business continuity, maintains customer trust, and drastically lowers the cost of any potential breach.
Conclusion
The “secret life” of a SOC is a cycle of constant vigilance, rapid response, and continuous improvement. As we’ve explored, the answer to what does a security operations center do is that it serves as the heartbeat of your digital defense.
In the high-stakes environment of Santa Clara and Silicon Valley, you can’t afford to wait for a breach to realize you need protection. At DataEndure, we specialize in making elite security accessible. We can deploy a full-scale SOC capability for your business in just 30 days, using our skilled experts to detect breaches in minutes and eliminate the alert fatigue that plagues traditional teams.
Don’t leave your organization’s future to chance. Secure your business with SOC-as-a-Service and let us take the watch.