Why Breach Hunting in Minutes Is Now a Business Survival Skill
Breach hunting in minutes is the practice of actively searching for attackers inside your network — and finding them fast enough to stop the damage before it spreads.
Here’s the short answer on how to do it:
- Detect signs of intrusion within 1 minute using EDR and SIEM telemetry
- Investigate the scope and behavior within 10 minutes using TTP-based and IOC-based hunt methods
- Contain the threat within 60 minutes before attackers move laterally across your network
The hard truth? Most organizations are nowhere near this.
The average breach goes undetected for 100 to 200+ days. By the time most security teams notice something is wrong, attackers have already escalated privileges, moved laterally, and exfiltrated data.
And attackers are getting faster.
A real-world test showed an AI-assisted attacker moving from an exposed credential to full AWS admin control in just 8 minutes. That’s not a worst-case scenario anymore — that’s the new normal.
The window to stop a breach is measured in minutes, not days. Once an attacker gets their first foothold, they have an average of just 1 hour and 58 minutes before they’ve moved through your entire network. Miss that window, and you’re no longer dealing with a breach — you’re dealing with a disaster.
For IT leaders in regulated industries, this isn’t just a technical problem. It’s a compliance risk, a financial exposure, and a reputational threat — all compressed into a 118-minute countdown.
This guide walks you through exactly how to build a breach hunting capability that works at the speed attackers move.
The Evolution of Breach Hunting in Minutes
In the “old days” of cybersecurity—say, way back in 2022—we used to talk about dwell time in terms of months. An attacker would slip in, set up a tent, and live in your network for half a year before anyone noticed. Today, that timeline has collapsed. As we navigate the landscape of April 2026, the speed of compromise has reached a terminal velocity that traditional security models simply can’t handle.
The most critical metric we track today is breakout time. This is the average time it takes for an intruder to jump from the initially compromised machine and move laterally through your network. Currently, that window sits at a mere 1 hour and 58 minutes.
If you aren’t engaging in breach hunting in minutes, you are essentially giving the keys to your kingdom to anyone who can pick a single lock. Once an attacker moves laterally, the complexity of the cleanup—and the potential for data exfiltration—skyrockets. This is why Threat Detection and Response has shifted from a “nice-to-have” audit requirement to a core operational necessity.
Recent scientific reviews of cyber threat hunting highlight that the “detect and respond” era is being replaced by a “hunt and contain” paradigm. We no longer wait for the alarm to go off; we assume the burglar is already in the house and we go looking for them.
Why Traditional Detection is Too Slow in 2026
Traditional detection relies on signatures and static rules. If an attacker uses a known virus, the alarm rings. But modern attackers don’t use known viruses. They use AI-assisted tools that can weaponize exposed credentials and gain full administrative control of a cloud environment in as little as 8 minutes.
We’ve seen reports of hackers stealing data in 72 minutes, which is faster than most people can finish a lunch break. If your SOC (Security Operations Center) relies on manual log review or a “we’ll check it tomorrow” mentality, the breach is over before you’ve even opened the ticket. Proactive Threat Hunting is the only way to close this gap.
The 1/10/60 Minute Challenge Explained
To survive this high-speed environment, we advocate for the 1/10/60 Minute Challenge. This is the gold standard for modern breach response:
- 1 Minute to Detect: You need automated systems that can surface a potential threat in sixty seconds or less.
- 10 Minutes to Understand: Within ten minutes, a human or AI-assisted analyst must determine if the threat is real, what it’s doing, and how it got there.
- 60 Minutes to Contain: Within the hour, the threat must be isolated. This beats the average breakout time and prevents the attacker from moving laterally.
Achieving this requires a specific stack of technology and expertise. When considering how to choose a threat detection tool, speed must be your primary filter.
Core Methodologies for Rapid Threat Detection
To achieve breach hunting in minutes, your team can’t just wander aimlessly through data. You need a structured approach. We generally categorize hunts into three main methodologies:
- Hypothesis-driven: “I suspect an attacker might be using PowerShell to exfiltrate data from our finance server. Let me look for those specific signs.”
- TTP-based (Tactics, Techniques, and Procedures): This focuses on how attackers behave. Since behaviors are harder for attackers to change than file hashes (IOCs), this is the most effective way to catch sophisticated actors.
- IOC-based (Indicators of Compromise): Hunting for known bad IP addresses, file hashes, or domain names. While fast, this is often reactive and less effective against “zero-day” or AI-driven attacks.
Modern platforms, such as those discussed in proactive threat hunting with Elastic, use AI to help validate these hypotheses in real-time, allowing analysts to pivot from a hunch to a confirmed finding in seconds.
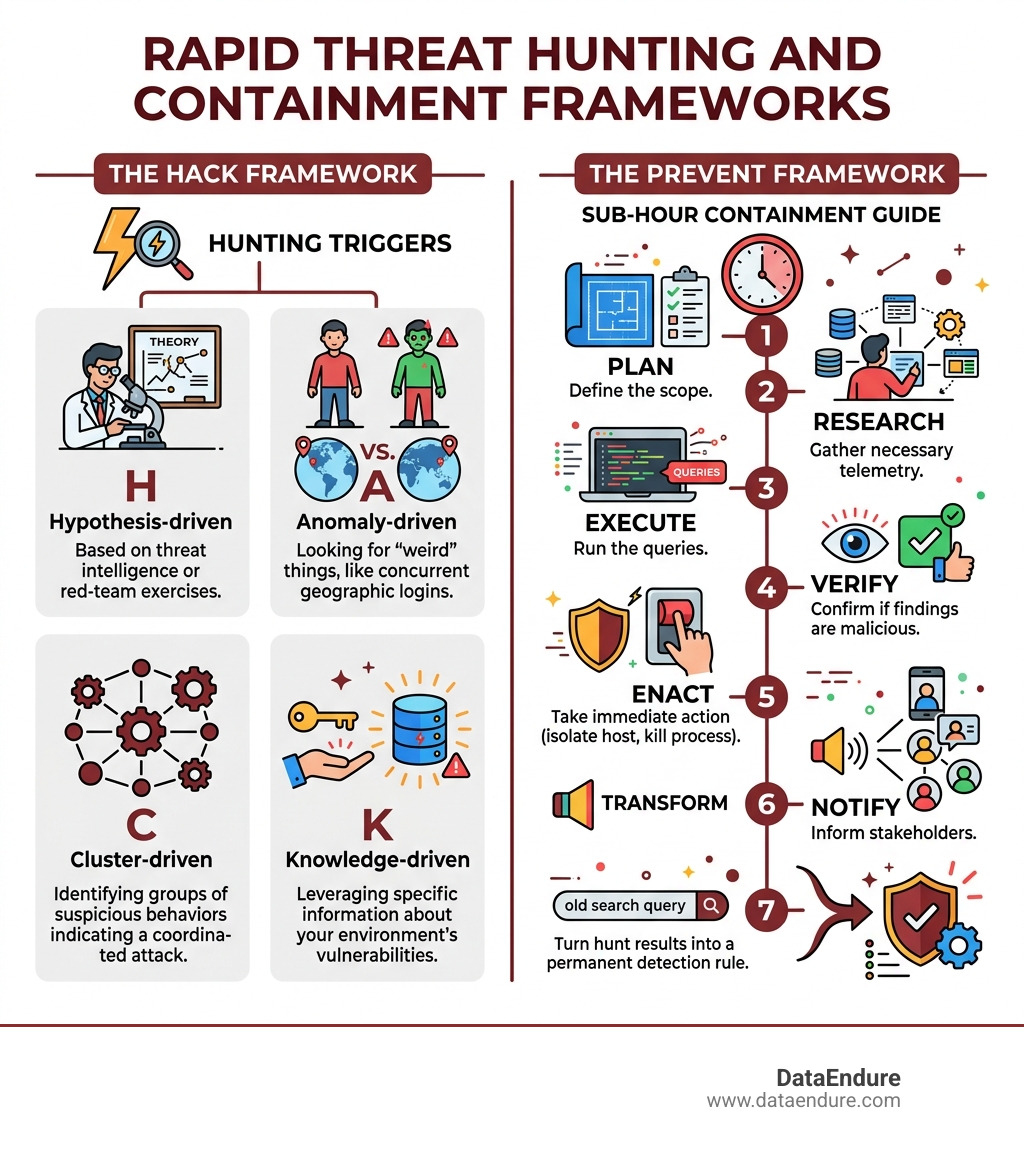
Implementing Breach Hunting in Minutes via the HACK Framework
To keep our hunting efforts organized, we use the HACK framework, which helps us identify the “triggers” for a hunt:
- Hypothesis-driven: Based on threat intelligence or red-team exercises.
- Anomaly-driven: Looking for “weird” things, like a user logging in from Santa Clara and Singapore at the same time.
- Cluster-driven: Identifying groups of suspicious behaviors that, when viewed together, indicate a coordinated attack.
- Knowledge-driven: Leveraging specific information about your environment’s vulnerabilities.
When you choose a threat detection tool, ensure it supports these diverse triggers so your team isn’t limited to just one way of finding trouble.
Using the PREVENT Framework for Sub-Hour Containment
Once a hunt is triggered, the PREVENT framework guides the execution:
- Plan: Define the scope.
- Research: Gather the necessary telemetry.
- Execute: Run the queries.
- Verify: Confirm if the findings are malicious.
- Enact: Take immediate action (isolate the host, kill the process).
- Notify: Inform the stakeholders.
- Transform: Turn the hunt results into a permanent detection rule.
This structured threat hunting methodology ensures that even under the pressure of a ticking clock, no steps are missed.
High-Value Hunt Areas to Prioritize
If you want to master breach hunting in minutes, you can’t look everywhere at once. You have to go where the attackers are most likely to hide. In 2026, that means focusing on identity and “living off the land” (LOTL) techniques.
Detecting Identity Anomalies and Breach Hunting in Minutes
Identity is the new perimeter. Attackers no longer “break in,” they “log in.” We look for:
- Coerced Authentications: Forcing a system to authenticate to a malicious server to steal credentials.
- DPAPI Key Theft: Stealing the keys used by Windows to protect everything from browser passwords to WiFi credentials.
- Non-Human Identities: Monitoring service accounts and Lambda functions. These are often overlooked and have high privileges.
Even experts aren’t immune; we recently saw a security expert Troy Hunt phishing attack that serves as a sobering reminder: if it can happen to the pros, it can happen to your admin team. Robust Endpoint Detection and Response is critical for surfacing these credential-based anomalies.
Monitoring Living off the Land (LOTL) Techniques
LOTL is the ultimate stealth tactic. Attackers use legitimate system tools (like PowerShell, WMI, or even AnyDesk) to carry out their dirty work. Because these tools are supposed to be there, traditional antivirus often ignores them.
To hunt LOTL in minutes:
- PowerShell Abuse: Look for encoded commands or scripts running from unusual paths.
- WMI Hijacking: Monitor for attackers using Windows Management Instrumentation to disable security software.
- AnyDesk/TeamViewer: Watch for remote access tools being installed on servers where they don’t belong.
Platforms like Microsoft Sentinel offer tools to conduct end-to-end threat hunting specifically designed to surface these “hidden in plain sight” behaviors.
Operationalizing Your Program for Maximum ROI
Building a program for breach hunting in minutes isn’t just about security; it’s about the bottom line. Gartner research from late 2025 shows that proactive threat hunting helps teams detect threats 11 days earlier and saves an average of $1.3M per incident.
| Metric | Manual Hunting | AI-Assisted Breach Hunting |
|---|---|---|
| Detection Time | Days to Months | 1 – 5 Minutes |
| Investigation Time | Hours to Days | 10 – 20 Minutes |
| Containment Time | Days | < 60 Minutes |
| Cost Per Incident | High ($4M+ average) | Significantly Lower (~$1.3M savings) |
| Skill Level Required | Tier 3 Senior Analyst | Tier 1/2 with AI Augmentation |
The risk of not hunting is high. Statistics show that 80% of ransomware victims suffer repeat attacks, often because the original entry point was never found and closed.
Integrating Hunting with Incident Response
Hunting and Incident Response (IR) are two sides of the same coin. Hunting finds the fire; IR puts it out. To meet the 60-minute containment goal, your threat detection and response tools must be integrated.
When a hunter finds a suspicious process, they should be able to isolate the host with a single click. This feedback loop ensures that every hunt makes the organization stronger by turning discoveries into automated alerts.
Overcoming Barriers to Rapid Response
The most common barriers to breach hunting in minutes are:
- The Skills Shortage: There aren’t enough senior hunters to go around.
- Alert Fatigue: SOC teams are buried under thousands of “maybe” alerts.
- Log Visibility: You can’t hunt what you can’t see.
We tackle these by using AI-assisted tools to filter the noise and by leveraging managed services that provide 24/7 coverage. As discussed in our Tech Talk on recurrent cyberattacks, understanding the patterns of how attackers return is key to breaking the cycle of compromise.
Frequently Asked Questions about Rapid Breach Hunting
What is the 1/10/60 Minute Challenge?
It is a framework for high-speed incident response: 1 minute to detect a threat, 10 minutes to investigate and understand its scope, and 60 minutes to contain it. Meeting this challenge is the only way to beat the average “breakout time” of an attacker.
How does breakout time impact hunting urgency?
Breakout time (currently averaging 1 hour and 58 minutes) is the window before an attacker moves from their initial entry point to other systems. If you don’t catch them within this window, the breach becomes significantly more difficult and expensive to contain.
Can AI tools really reduce dwell time to minutes?
Yes. AI-assisted tools can correlate millions of data points in seconds, identifying TTPs and anomalies that would take a human analyst days to find. This allows for breach hunting in minutes by surfacing the “signal” within the “noise” almost instantly.
Conclusion
The era of waiting for an alert to pop up is over. In 2026, if you aren’t hunting, you’re already compromised—you just don’t know it yet. Mastering breach hunting in minutes is about reclaiming the advantage from the attacker and closing the window of opportunity before they can move laterally.
At DataEndure, we specialize in helping organizations reach the 1/10/60 goal. Our managed cybersecurity solutions are designed to deploy in just 30 days, providing the skilled experts and advanced technology needed to reduce alert fatigue and stop breaches in their tracks.
Don’t wait for the 118-minute countdown to start. Be proactive, be fast, and stay resilient. Explore how we can help you master Threat Detection and Response and secure your future.